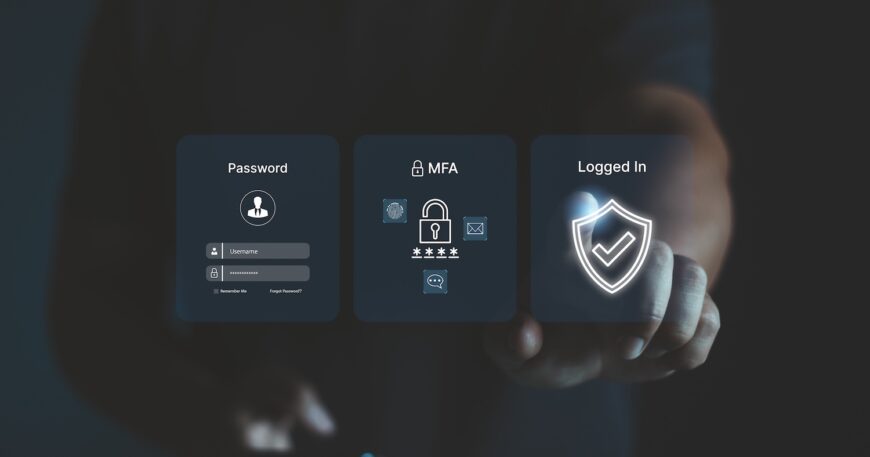
In today’s rapidly evolving digital landscape, the days of relying solely on passwords for authentication are numbered. Multi-factor authentication (MFA) is becoming the standard for securing accounts and data. MFA adds an extra layer of security by requiring users to provide multiple forms of verification, such as something they know (a password), something they have (a smartphone), and something they are (biometrics).
The Basics of Multi-Factor Authentication
Multi-factor authentication is a security measure that requires users to confirm their identity through multiple verification methods. These methods typically fall into three categories:
- Something You Know: This includes passwords or PINs. While passwords are a common form of authentication, they are often vulnerable to attacks such as phishing and brute force[1].
- Something You Have: This involves physical items like smartphones or security tokens. For example, a verification code sent to your smartphone adds a layer of physical security[2].
- Something You Are: This encompasses biometric data such as fingerprints, facial recognition, or voice recognition. Biometric methods are difficult for unauthorized users to replicate[2].
The Rise of MFA in 2025
In 2025, MFA will be a non-negotiable security measure for businesses and individuals alike. It significantly reduces the risk of unauthorized access, making it a critical component of cybersecurity strategy. Here are some key trends and predictions for MFA in the coming year:
- Widespread Adoption: MFA adoption is expected to surge as organizations prioritize safeguarding sensitive data. According to recent statistics, 87% of companies with over 10,000 employees already use MFA, and this number is set to increase[3]. Small to medium-sized businesses (SMBs) are also catching up, with a growing trend towards MFA implementation[3].
- Passwordless Authentication: The traditional password is rapidly becoming obsolete due to its vulnerabilities. Passwordless authentication methods, such as biometrics and hardware tokens, are expected to become mainstream[4]. These methods offer enhanced security and user convenience, eliminating the risks associated with compromised credentials[4].
- AI-Driven Adaptive Authentication: Artificial Intelligence (AI) will play a pivotal role in adaptive authentication systems. These systems tailor the verification process based on user behavior and contextual factors, providing dynamic security without unnecessary friction[4]. For example, a low-risk login attempt from a familiar device might require a single factor, while a high-risk attempt prompts additional verifications[4].
- Blockchain and Decentralized Identity: Decentralized identity systems, powered by blockchain technology, are emerging as a game-changer. These systems grant users ownership of their digital identities, reducing dependence on centralized databases that are vulnerable to breaches[4]. Distributed ledgers store identity credentials, enabling individuals to share only necessary data securely[4].
- Securing the Internet of Things (IoT): The proliferation of IoT devices necessitates robust authentication measures. Multi-layered authentication for IoT will help secure devices against unauthorized access, ensuring data integrity and privacy[4]. With IoT ecosystems predicted to reach over 44 billion devices globally by 2030, MFA will be crucial in protecting these interconnected systems[4].
Benefits of Multi-Factor Authentication
- Enhanced Security: MFA protects against advanced cyber threats by reducing the attack surface. By verifying every access request and limiting privileges, organizations can better safeguard their data and systems[1].
- Improved Compliance: MFA helps meet regulatory requirements by ensuring data privacy and security. Adopting this model can simplify compliance with standards such as GDPR, HIPAA, and PCI DSS[3].
- Increased Productivity: Streamlining access to resources and reducing security friction for users can enhance productivity. Employees can access the tools they need without unnecessary delays, while still maintaining robust security[3].
- Reduced Risk: MFA minimizes the impact of potential breaches by limiting the scope of damage. By isolating network segments and continuously monitoring for threats, organizations can contain and address incidents more effectively[2].
Next Steps for Implementing MFA
- Evaluate Your Current Security Posture: Assess your organization’s existing security controls and identify gaps. Understanding your current vulnerabilities is the first step towards strengthening your defenses[3].
- Choose the Right MFA Solutions: Select tools that align with your specific needs and budget. There are various MFA solutions available, so it’s important to choose those that best fit your organization’s requirements[3].
- Implement a Phased Approach: Start with high-value assets and gradually expand your MFA implementation. This method allows for a smoother transition and ensures that critical resources are protected first[3].
- Continuously Monitor and Adapt: Stay informed about the latest threats and adjust your security strategy accordingly. Cybersecurity is an ongoing process, and organizations must remain vigilant to protect against emerging risks[3].
By embracing multi-factor authentication, you can significantly enhance the security of your digital workspace and protect your organization from future cyber threats. This proactive approach not only safeguards your data but also fosters a culture of security-first thinking within your organization.
References
[1] What is: Multifactor Authentication – Microsoft Support
[2] What are MFA Examples and Methods? – Palo Alto Networks
[3] Multi-Factor Authentication (MFA) Statistics You Need To Know In 2025
